Secure your software supply chain at the source.
Because scanning and justifying after the fact isn’t supply chain security.
Because scanning and justifying after the fact isn’t supply chain security.
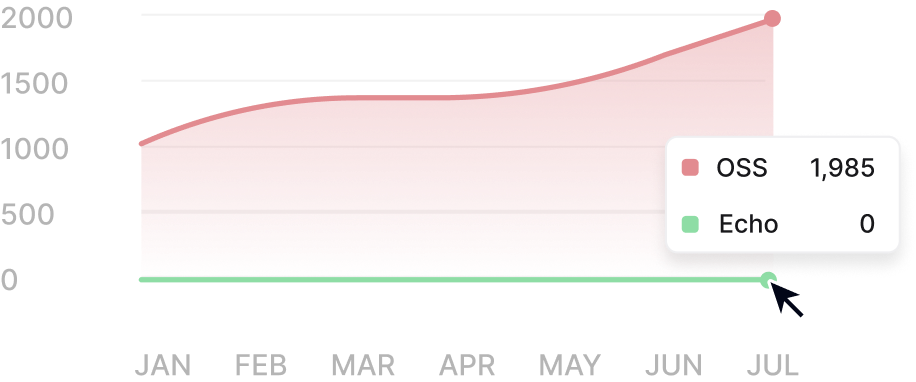
Echo’s secure artifacts are drop-in replacements for vulnerable open source components that ripple vulnerabilities across your pipelines, scans, and audits.
"Echo has enabled us to proactively secure our software supply chain with confidence."

Yechezkel RabinovichCTO

Eliminate vulnerabilities that stall security reviews and procurement.
Customers can scan clean with their own tools – no waivers or overrides required.
Ensure your images pass customer scans across environments and scanners.

Every change is versioned, reviewed, and fully traceable from source to final image.

Builds run in hardened, isolated environments with ephemeral workers.

Fixes are applied selectively to reduce risk without introducing breaking changes.

Every image is signed at build time and shipped with a corresponding SBOM.

Each build includes full provenance and attestation metadata for downstream validation.

Each image includes VEX data to clearly communicate vulnerability status and impact, so scanners and auditors understand what applies – and what doesn’t.

Images only move to production after automated verification and policy checks pass.

Images are continuously re-evaluated as new vulnerabilities and fixes emerge.
All vulnerabilities are triaged within 24 hours. Critical/high are patched in up to 7 days and medium/low within 10 days.
Your private registry automatically pulls our patched images and libraries so that you’re always using the latest clean version.
Our backports let you stay with artifact versions that work best for you, without forcing risky upgrades.
Echo uniquely ensures visibility into both fixed and unresolved vulnerabilities for the most accurate risk assessment.
With Echo, eliminate the vulnerability chase for your engineers right at the source.